There is a password reset vulnerability caused by a data leak from a debug log file in the WordPress plugin Easy WP SMTP.
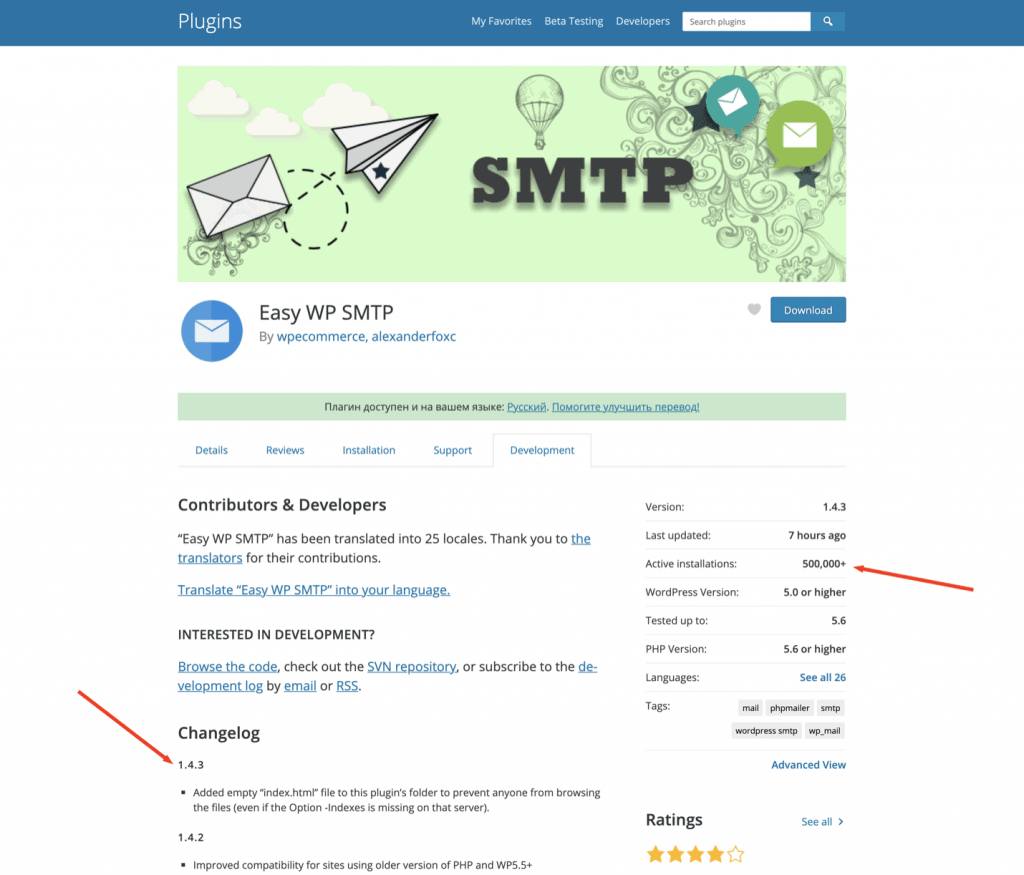
Several hours ago, “WP eCommerce” released Easy WP SMTP WordPress plugin version 1.4.3 which patches the easily exploitable and dangerous vulnerability found by NinTechNet.
See all Easy WP SMTP vulnerabilities.
It appears that Easy WP SMTP plugin version 1.4.2 and older versions are vulnerable due to sensitive information disclosure. This plugin has more than 500,000 active installs.
Vulnerability type
Unauthenticated admin password reset
Fixed in version
1.4.3
Sites affected
500 000+
It is hard to determine the actual number of vulnerable installations because there are several prerequisites in order to exploit the vulnerability.
Vulnerability in Easy WP SMTP WordPress plugin
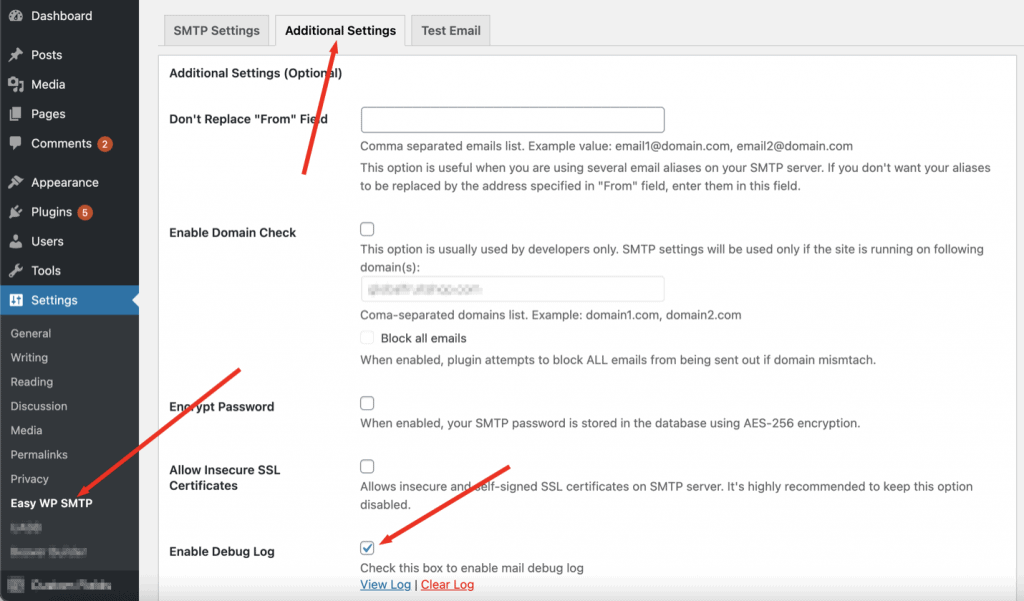
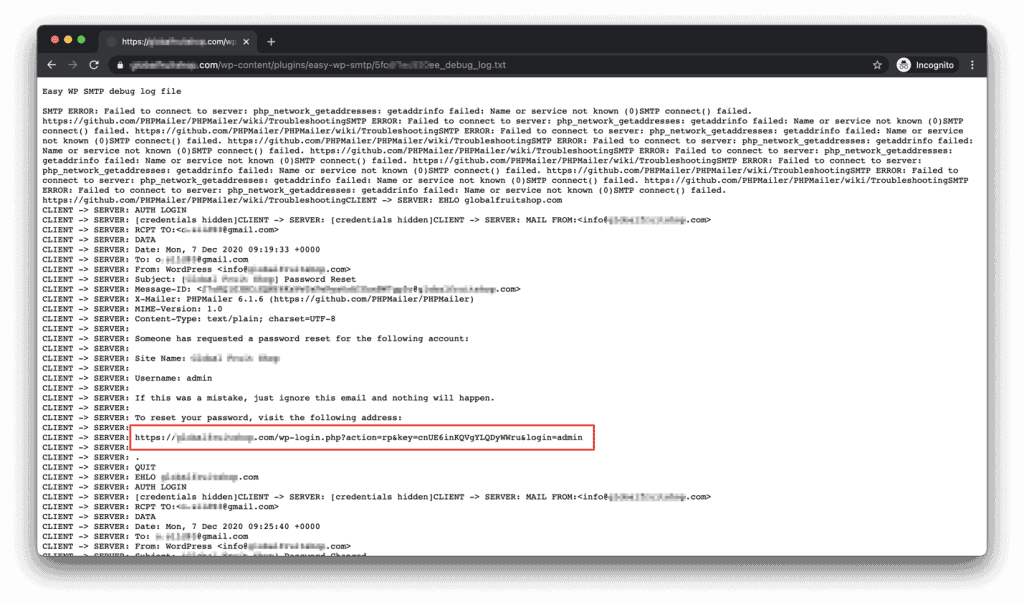
First we should mention that Easy WP SMTP has a debug log function. When enabled, this function will write all the information about WordPress emails to a .txt file and also includes the email content in plain text format. The content of these emails is the most significant threat in this case.
WordPress will send an email with a temporary custom link when you initiate the password reset procedure, and the link leads to a password reset form which allows you to set a new password for the account.
This method is safe as long as the mailing system is safe and no one except the real user can get those emails with password restoration links. It turned out that the Easy WP SMTP plugin doesn’t have essential protection for its main directory content.
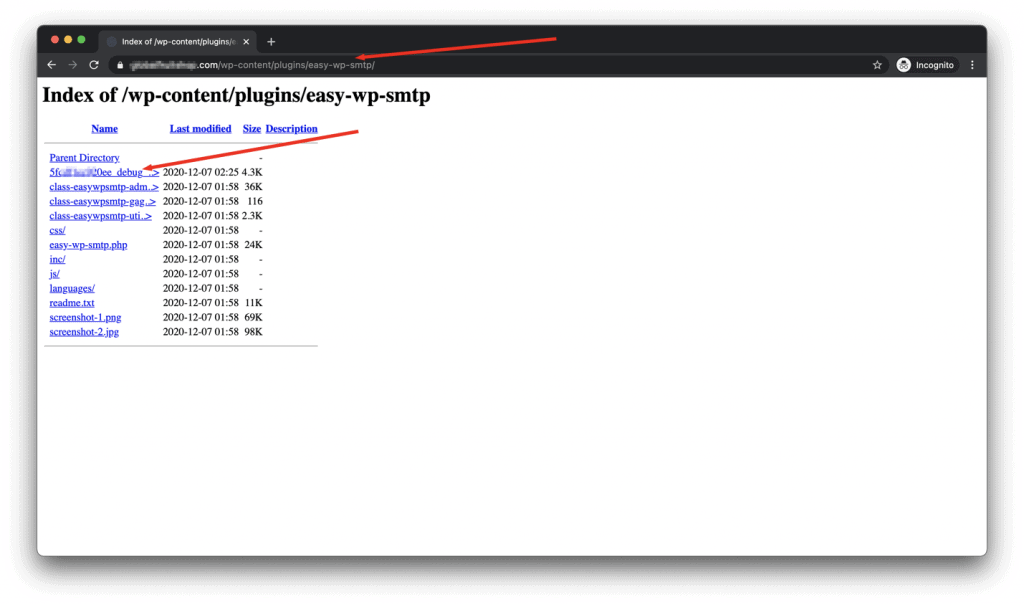
It appears that the Easy WP SMTP plugin initially doesn’t include any index.html or index.php file in its main directory where these log files are stored.
It is not a problem on sites hosted on servers with a sufficiently secure configuration and on sites with other security hardening measures or tools that prevent directory listing. But if the server configuration allows directory listing and there are no other factors that would prevent it, there could be a security risk.
In this case, we can see all the files and directories, including the log file, which contains the sensitive information.
There are several prerequisites: the log function is enabled, the directory is accessible, all that remains is to enumerate or guess the username or email whose password we will try to reset.
Now we can initiate a password reset procedure by visiting the WordPress login form and pressing the “Lost your password?” link that will allow us to enter the username or email of the user whose password we want to reset.
Right after, WordPress will send the email which will contain a password reset link. Now the log file will contain the contents of that email, and it means everyone could read it and use the link to reset the password. An attacker can reset a password for any user with any privileges. The vulnerability is not restricted to any specific user name or user role.
As you can see, this vulnerability is easy to exploit. It does not require any special knowledge, making it even more dangerous.
Solution
While you can update the plugin to the latest available version (1.4.3) which solves the directory listing, we believe that it needs a little more if you still want to keep the logging function turned on.
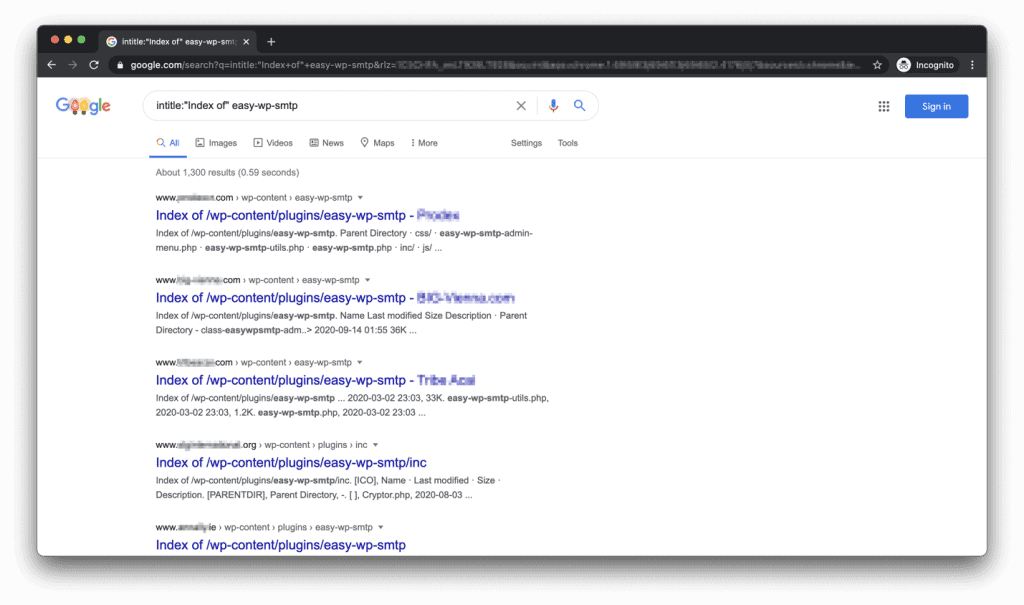
In most cases, the plugin directory might be indexed by Google and possibly other search engines. Having directory listing turned off will not prevent sensitive data leaks if the attacker can get the real log file name from SERP’s.
If an attacker knows the full path to the log files, they can access it directly, even with directory listing disabled.
If you have Patchstack installed, you are protected from this vulnerability, but it is always strongly advised to update or delete vulnerable plugins from your site.
We suggest everyone update the plugin, disable directory listing on your site through the server configuration or .htaccess file tweaks.
What makes the issue worse is that even if you turn the logging function off, delete the old log file, and turn the logging function back on – the new log file will have the same name and it will be possible to find the name of the file from Google cached results and still access it directly (even with the directory listing disabled).
Disabling directory listing on your site
Directory listing function is a part of the web-server configuration. In case you have noticed that your server configuration allows directory listing, but you do not have the rights to change the server configuration, you could override some parameters by adding small code snippets to your .htaccess file.
To disable the directory listing, you should add this line to your .htaccess file located in the root (main) directory of your website:
Options -IndexesWe recommend doing this because attackers might use directory listing for reconnaissance and other attacks.
Timeline
06.12.2020 – Public exploitation detected by https://profiles.wordpress.org/mathieg2/
07.12.2020 – Plugin received a patch 1.4.3 (added index.html to directory)
Known IOCs
212.227.174.234
41.230.236.11
20.62.40.13
If you want to protect your site, we can help – contact Patchsack support by clicking on the chat bubble on the bottom right (some ad-blockers can disable it).