There are different options when it comes to choosing a web application firewall for your website. In this article, we will cover endpoint firewall vs cloud firewall.
The technical approaches have various pros and cons and tend to be more effective in different situations.
Let's see what's the main difference between the technologies and discuss their strengths and weaknesses. Ultimately, let's try to figure out which one to use for a website.
What is a cloud-based firewall (DNS, reverse proxy)?
The cloud-based firewall works as a middle-man between your site and the visitor. When the visitor enters your domain name to the browser, the connection, in reality, goes to the cloud-based firewall providers' servers, where it's analyzed.
If all the checks pass and the visitor is legitimate and does not pose any risk to the site, the traffic is forwarded to the actual website (or to the cached version of the site).
You probably have heard about Cloudflare. They are the most known cloud-based firewall provider.
Advantages of a cloud-based firewall (cloud WAF)
Cloud-based firewalls often analyze a wider spectrum of traffic, since everything that is sent to the domain has to pass the cloud-based WAF servers. One of the advantages is protection against DDoS attacks.
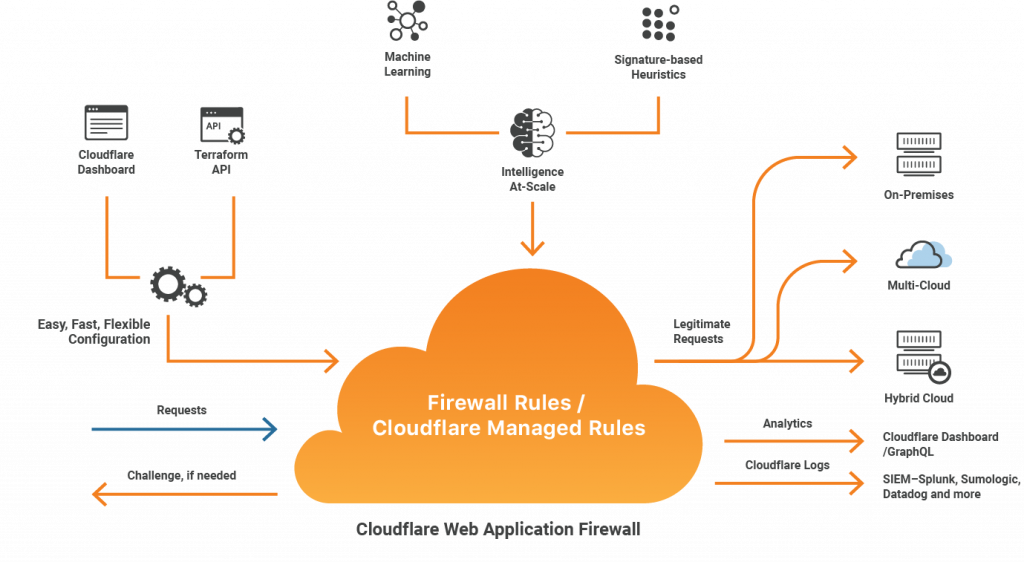
Another thing to note is the fact that cloud-based firewalls often save your server resources from unwanted traffic even before accessing the site itself.
Disadvantages of a cloud-based firewall (cloud WAF)
Of course, cloud-based firewalls also have their weaker side. One of them would be the fact the cloud-based firewalls really don't know who the visitor really is.
The cloud-based firewall has no understanding of how the site works, what are the software-specific circumstances, who is authenticated, and which permissions they have.
Because cloud-based firewalls have often generic use cases, many software-specific vulnerabilities (such as plugin vulnerabilities) might not be blocked.
Sites behind a cloud-based firewall also rely completely on the service provider. If the cloud-based firewall provider has service downtime, your site will be down as well.
In many cases, cloud-based firewalls can also be bypassed completely if the site is accessed directly via IP rather than via domain name.
What is an endpoint web application firewall (endpoint WAF)?
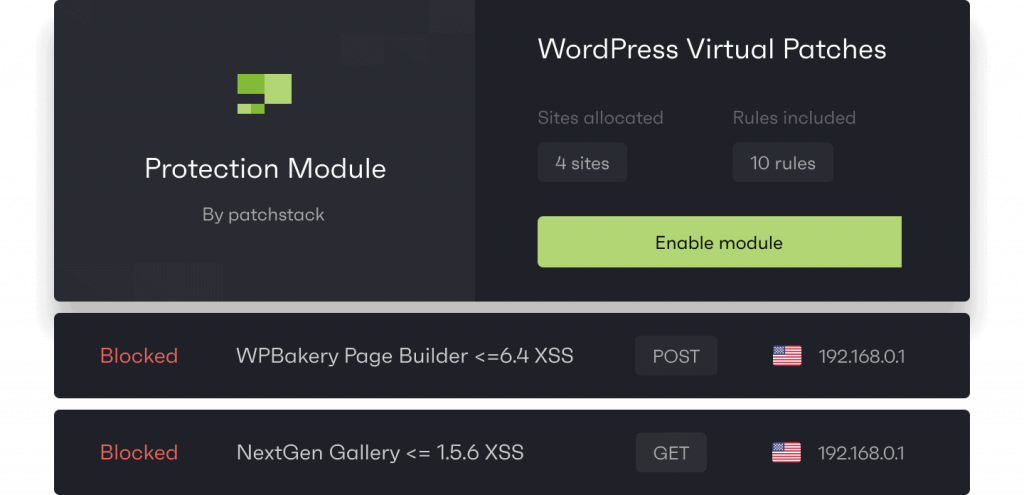
Endpoint web application firewall (Endpoint WAF) runs within the application itself. It's aware of the software used inside the website and understands how it's built.
Endpoint firewall understands how the software used inside the website works and who are the visitors by their permissions and if they are authenticated or not.
Most next-gen firewalls that are available today, also work on the endpoint, because they can do more.
Advantages of an endpoint firewall (endpoint WAF)
Endpoint firewalls tend to have fewer false positives and can be more effective in blocking more complicated and software-targeted attacks.
Endpoint WAFs often combine signature-based and heuristic protection, some even include behavioral analysis.
Since the endpoint firewall has all the information about the websites' technical environment and software specifics, it's multifunctional and capable of serving the role of IDS (intrusion detection system) and IPS (intrusion prevention system).
You're also not affected if the endpoint WAF provider service drops, you might not receive the new rules, but the firewall and the site will remain working. It also can't be bypassed like cloud WAFs since it's running inside the website itself.
Disadvantages of an endpoint firewall (endpoint WAF)
The main disadvantage is that the endpoint firewall runs on your own resources. The traffic hits your site, and it's being analyzed there, which can require slightly beefier infrastructure for high-traffic sites.
Endpoint WAFs usually don't have DDoS protection, especially when applied to the application (not deep within the server).
Which one to choose? Cloud firewall or endpoint firewall?
The truth is, you should use both. While they have their pros and cons, it's always good to have multiple layers of security for the sites.
Cloud WAF for reducing bot traffic and preventing DDoS attacks, and Endpoint WAF for protecting the website from hacking attempts.
We always suggest a combination of Cloudflare Free (cloud WAF) and Patchstack (endpoint WAF) for a good layered website security strategy.
Frequently asked questions about endpoint firewalls and cloud-based firewalls
What is an endpoint WAF?
The endpoint web application firewall (endpoint WAF) is a firewall that runs within the application. It's aware of the software used inside the website and understands how it's built.
What is cloud WAF?
The cloud-based firewall works as a middle-man between your site and the visitor. When the visitor enters your domain name to the browser, the connection, in reality, goes to the cloud-based firewall providers' servers, where it's analyzed.
If all the checks pass and the visitor is legitimate and does not pose any risk to the site, the traffic is forwarded to the actual website (or to the cached version of the site).
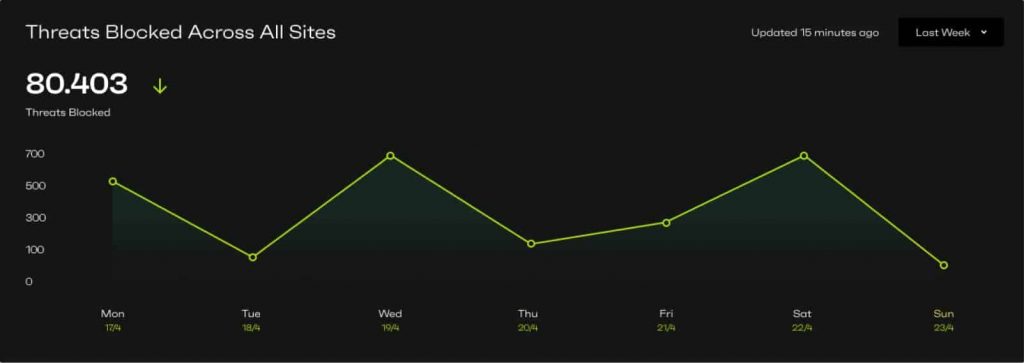
How do I check if my firewall is blocking attacks?
The best way to check is usually the firewall logs. Each firewall provider will have its own way of showing the data.
What are the advantages of an endpoint firewall?
Endpoint firewalls tend to have fewer false positives and can be more effective in blocking more complicated and software-targeted attacks.
Which firewall to choose (endpoint or cloud-based)?
The truth is, you should use both. While they have their pros and cons, it's always good to have multiple layers of security for the site. cloud WAF for reducing bot traffic and preventing DDoS attacks, and endpoint WAF for protecting the website from hacking attempts.
We always suggest a combination of Cloudflare free (cloud WAF) and Patchstack (endpoint WAF) for a good layered website security strategy.





