Logs for WordPress administrators – the definitive guide to all the logs WordPress site administrators can use.
Logs are like unsung heroes; they store a wealth of information and have an important role in any type of software, yet they are often ignored.
This quote from the PCI DSS compliance regulations highlights how important logs are for the security of websites:
Logging mechanisms and the ability to track user activities are critical in preventing, detecting, or minimizing the impact of a data compromise.
In this article, we will explain what logs are, what information you can find in them, and how you can use this information to better manage and improve the security of your WordPress websites. Let’s dive right in.
Introduction to WordPress logs
Logs are records of events related to a given software, application, or service. Most modern software products keep logs of some kind. This means everything from your smartphone to a smart fridge to a web server keeps a log.
Logs are usually kept in plaintext files with a .txt or .log file extension, although this isn’t a hard rule. The files that contain logs are referred to as log files.

Data you can find in web server and web application log files include but are not limited to error messages, HTTP request details, connections to the server, and database transactions. Entries in log files are timestamped so you can determine when an event occurred down to the second (or even fractions of a second).
Why do we use logs?
While the description of logs makes their usefulness to developers clear, do they have any value for WordPress site admins? Absolutely. Here are some of the most common uses of logs from the perspective of a WordPress admin.
Simplify troubleshooting
Logs make troubleshooting issues significantly easier. In some cases, an error message serves as a breadcrumb that inches you closer to solving a problem. In other words, logs may give you exactly what you need to resolve an issue, they make it hard to troubleshoot issues into “Googleable” problems.
Case in point: knowing your e-mail issue is related to the SMTP (Simple Mail Transfer Protocol) message “Error Must issue a STARTTLS command first” makes fixing it much easier than just knowing you can’t send emails. Even if you don’t know exactly what the error means, your Googling becomes much more targeted.
Improve marketing & SEO
Logs are all about aggregating data. The obvious marketing benefit here is the ability to compile and analyze data about the number of visitors to your site, the pages they visit, and where they are connecting from.

Logs are also of great help with technical SEO. If your site returns a lot of HTTP error codes, such as it responds with too many 302 redirects, or a page with great content has low crawl priority, your website’s SEO will suffer.
Analyzing log files enables you to track bot activity, HTTP errors, and redirects, thus fixing these issues.
Increase user accountability
Once a WordPress site reaches the scale where multiple users are making changes, such as an e-commerce store, accountability becomes important.
A WordPress audit trail (activity log) enables you to determine who made changes and what changes were made. Not only does this improve accountability, but it may also enable you to realize some users have a role with more privileges than they need (proactive security).
Enhance WordPress security
Building on the accountability point, logs can help enhance overall WordPress security. Once a WordPress site is on the Internet, taking security seriously is a must.
Logs can help you be proactive in detecting and preventing malicious behavior. In the event of a breach, logs can also help you determine how widespread the damage was and which vulnerability the attackers exploited.
Meet compliance requirements
For organizations subject to strict regulatory standards, logging may be a requirement. For example, WordPress e-commerce sites need to be PCI DSS (Payment Card Industry Data Security Standard) compliant.

These regulations have requirements pertaining to how long logs must be retained and the type of data that must be recorded in them.
Different logs for WordPress site admins
Now that we understand what logs are at a high level and why as a WordPress site administrator you should care about them, let’s dive into what specific logs you should be aware of.
Web server service logs
Web server logs provide a ton of value to WordPress administrators. While WordPress can be run on almost any server that supports PHP and MySQL, most WordPress websites run on either Apache or Nginx. Given that, we’ll focus on these two web servers here.
The two most important log files for both Apache and Nginx are:
- access.log: The access.log file contains a record of all requests processed by the webserver. Here you’ll find data like HTTP Response Codes, source IP addresses, timestamps, the type of request the client made (GET, POST, etc), and more.
- error.log: The error.log is exactly what you’d expect: a log file where the webserver records errors. Messages in this log can indicate problems such as an issue with the webserver configuration or an error that occurred when a client requested a URL that the server for some reason could not parse properly.
It is important to point out that the verbosity of web server log files is configurable. Therefore if you need to see more about what is happening on your website, you can always increase the logs’ verbosity from the webserver configuration.
Firewall logs
A firewall is an important part of keeping a server secure. In the world of WordPress administration, WAFs (Web Application Firewalls) are used to protect sites.
There’s no specific standard for where and how a firewall will record events, but most do. Data commonly found in firewall logs include:
- Source IP address of an attempted connection,
- The protocol used during the connection attempt: TCP (Transmission Control Protocol) or UDP (User Datagram Protocol),
- Port the connection attempt was made to (e.g. 22 for SSH, 443 for HTTPS),
- Reasons for a block (e.g. too many connection attempts in a short window of time or violation of a firewall rule).

These logs are important because they help you identify malicious behavior such as aggressive scans, and also abnormal trends, and potentially false-positive blocks.
FTP/SFTP logs
As a WordPress admin, you’re likely familiar with FTP (File Transfer Protocol) and SFTP (SSH File Transfer Protocol). You should ALWAYS use SFTP instead of FTP.
Logs from your FTP/SFTP client (e.g. FileZilla or CyberDuck) can help with troubleshooting client-side issues. However, server logs can provide even more information.
The FTP/SFTP server running on your site will record the IP address & username of the client connecting, timestamps of connections, file transfers, and modifications, enabling you to see what activity has occurred.
Security tip: this is where file integrity monitoring solutions help as well.
WordPress audit logs
Audit logs are sometimes referred to as activity logs, security logs, or audit trails. A WordPress audit log keeps a record of changes on a site or on the child sites, in the case of a multisite network.
In a nutshell, a WordPress audit log records timestamped information, including the IP address, username, and role, such as who:
- published or edited a post,
- made changes to plugins or themes,
- modified files,
- logged in,
- and much more.
WordPress does not have out-of-the-box logging capabilities. In this case, you need a WordPress activity log plugin or you can use Patchstack.
Keep in mind, that the level of detail and coverage of what the plugin keeps a log of depends on which plugin you use. If you want a separate plugin for logs, we kindly recommend the WP Activity Log.
The vital role of logs in security
Logs go a long way in enabling WordPress site security. At a high level, there are two types of security:
- Proactive security focuses on preventing security breaches from occurring.
- Reactive security focuses on mitigating damage and determining the scope of a breach.
Using logs for proactive WordPress security
Logs go a long way in identifying how attackers are trying to breach your site. If you see constant attempts to access yoursite.com/wp-admin/ from the other side of the world, that may suggest someone is trying to brute-force attack your site.
If you see these attempts with your username, it’s possible the attacker knows your username, but not your password.
Additionally, because actions can be triggered based on log entries, your intrusion prevention system (IPS) or intrusion detection system (IDS) can be configured to act based on the information in the logs.
For example, the WP ActivitytLog plugin can be used to build an effective WordPress intrusion detection system (IDS). Patchstack can also be a good combination of IPS and IDS on your website endpoint.
Another good example of an effective IPS that uses logs is the open-source project Fail2Ban.
Using logs for reactive WordPress security
In the event your website is breached, logs enable you to see how the hackers got in, and what they did. Not only does this allow you to evaluate the scope of the breach, but it also helps you determine what went wrong.
If an unpatched webserver was the root cause, you can update it. If you used a weak password, you can create a more robust password policy or enable multifactor authentication.
Where can you find all these logs?
Now that we’ve covered what logs are and why they are important, let’s dive into where you can find them.
WordPress activity log in WP Activity Log plugin
The WordPress activity logs generated by the WP Activity Log plugin are viewable from the WordPress dashboard.
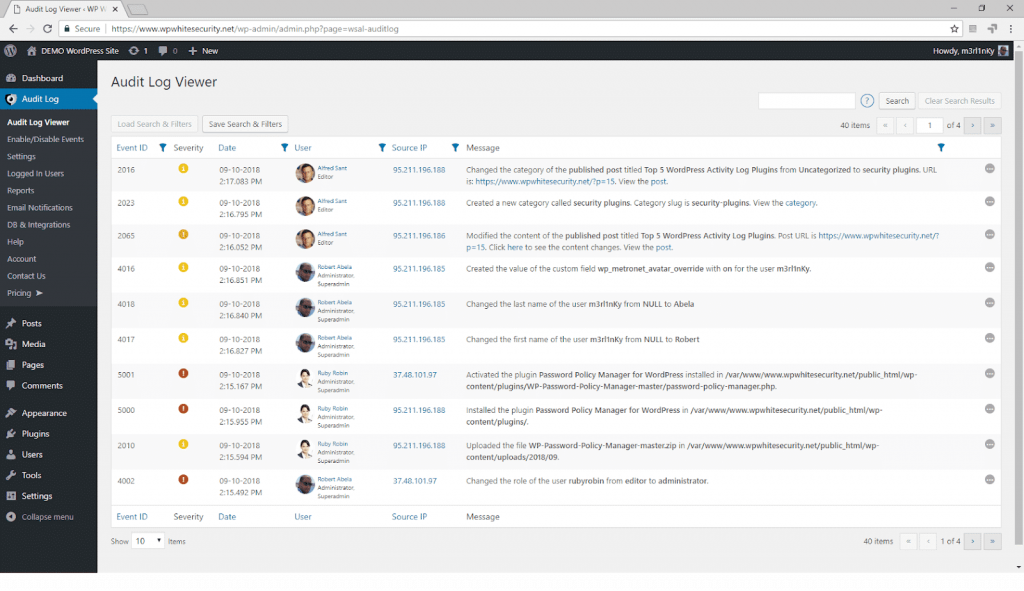
Unlike most other log files, WordPress activity logs are stored in a database. The plugin stores data in a database because in this case it is much faster and requires fewer resources.
If you keep an activity log on your WordPress, you are interested in learning more about what your users are doing, and what is happening on your website. However, no one really has the time to browse through the logs, looking for information.
The good news is that you do not need to have time. You can configure the WP Activity Log to send you daily, weekly, monthly, and even quarterly reports. You can create your own report criteria, so it is up to you what type of update you want.
On top of that, you can also configure the plugin to mirror the WordPress activity logs to Slack, or another central logging system of your choice.
Web server service logs
Web server access logs are generally viewable by using a GUI-based tool like Plesk or phpMyAdmin, or by using a text editor such as NotePad++ or vim.
The location of the access.log and error.log files can vary, but they are often found in the following locations:
| Operating system | NGINX | Apache |
|---|---|---|
| FreeBSD | /var/log/nginx-access.log and /var/log/nginx-error.log | /var/log/httpd/httpd-access.log and /var/log/httpd/httpd-error.log |
| Debian, Ubuntu, etc. | /var/log/nginx/error.log and /var/log/nginx/error.log | /var/log/httpd/access_log and /var/log/httpd/error_log |
| CentOS, RedHat, Fedora, etc. | /var/log/nginx/access.log and /var/log/nginx/error.log | /var/log/apache2/access.log and /var/log/apache2/error.log |
Let’s dive into some examples of what you may see in these logs.
access.log
In this log, you will find data including visitor IP address, pages viewed, the type of browser making the request, and HTTP status codes.
Below is an example access.log entry detailing a request from someone with IP address 10.10.10.10 using Firefox version 68 on Windows 10. We also see that the HTTP status code was 200, which means there were no errors.
10.10.10.10 - - [23/Aug/2019:21:17:34 +0000] "GET /news/excitingstuff.html HTTP/1.1" 200 559 "http://192.168.100.1/mainpage.html" "Mozilla/5.0 (Windows NT 10.0; WOW64; rv:68.0) Gecko/20100101 Firefox/68.0"Refer to Wikipedia for a complete list of HTTP status codes and a description of what they all mean.
error.log
The Apache docs call this the most important log file. Errors recorded here may be minor and not impact site performance. However, there can also be errors that are related to an issue impacting your site’s performance or even security.
The error.log file records are fairly verbose but human-readable. Here’s an example of an error.log entry that doesn’t necessarily imply a problem with the site, it tells us the version of OpenSSL the server is using:
[Wed Aug 21 00:17:03.468136 2019] [mpm_event:notice] [pid 2467:tid 3069632512] AH00012: Apache/2.4.18 (RedHat) OpenSSL/1.0.2g configured -- resuming normal operationsFTP/SFTP server logs
The specifics of your FTP/SFTP server logs will vary depending on the service running on the webserver hosting your WordPress site. OpenSSH is one of the more popular SFTP servers, and it logs to the auth.log log file, which can be found on many *nix operating systems.
This means from the Linux command line, the command grep 'sshd' /var/log/auth.log or similar can display SFTP information stored in the log. If you are an advanced user and want to set up logging of SFTP commands, check out this RedHat article.
Regardless of the FTP/SFTP server you use, the value of reviewing the logs is simple: properly configured FTP/SFTP logs enable you to see who accessed and modified what files. Not only does this enhance accountability, but it also enables security.
Firewall logs
The location of firewall logs will vary significantly by the vendor. If you have your own VPS, a good first place to check is the /var/log/ directory.
If you are not sure there the solution keeps logs, defer to the provider’s documentation. If you're using Patchstack, just log in to your app to see all the logs.
The important part of firewall logs is they enable you to see what the firewall blocked and why. Generally, you’ll see verbiage including the word “block” or “blocked” along with a timestamp and IP address in firewall logs. This will often come along with information like a policy violation or reason for the block.
How to use logs effectively
Logs are a valuable tool. As an administrator, you need to know what to look for to make them effective.

This means having a baseline understanding of what to expect, looking at the right logs for a given problem, and knowing how to parse for warning/error/critical messages and keywords (e.g. searching for a given username, web page, or HTTP code).
Let’s walk through a few simple examples to drive the points home.
Identifying malicious behavior and tracking users through logs
There is no magic bullet to how you can use logs to identify malicious behavior or spot a hack attack. It all depends on the nature of the website and how your users work etc.
As an administrator of a WordPress website familiarizes yourself with what is running on your website, who logs in from where and when, who typically installs new plugins or updates them etc.
Only when you are familiar with your setup and with the norms of the website you can start spotting suspicious activity.
It is important to point out that you won’t find all the information you need in one log file when doing an analysis.
Like a puzzle, you must use bits and pieces from different log files to paint a complete picture of what happened in a hacker attack, or what caused a technical issue.

Logs are a must in WordPress security
As we have seen, logs provide a wealth of information to WordPress administrators. However, you can only find what you need if you know what you are looking for.
Hence why it is of utmost importance that you:
- know about the log files available and what information is logged in them,
- familiarize yourself with the way things work and who does what on the WordPress website you manage.
In this article we have provided you with a lot of information about logs, which coupled with your knowledge of your site, you should be able to get started and better manage and secure your website straight away.
Frequently asked questions about logs for WordPress
How to view WordPress error logs?
To look at your WordPress error logs you need to navigate to your /wp-content/ folder in your File Manager. There you need to locate the debug. log file. This is the file that will contain all WordPress errors, warnings, and notices that were logged.
Why are logs important in WordPress?
Logs provide a wealth of information to WordPress administrators - they help simplify troubleshooting, they help in improving marketing & SEO, they help to determine who made changes in your WordPress site and what changes were made, and much more.
Where can you find FTP/SFTP server logs?
The specifics of your FTP/SFTP server logs will vary depending on the service running on the webserver hosting your WordPress site. OpenSSH is one of the more popular SFTP servers, and it logs to the auth.log log file, which can be found on many *nix operating systems.
This means from the Linux command line, the command grep 'sshd' /var/log/auth.log or similar can display SFTP information stored in the log. If you are an advanced user and want to set up logging of SFTP commands, check out this RedHat article.
Regardless of the FTP/SFTP server you use, the value of reviewing the logs is simple: properly configured FTP/SFTP logs enable you to see who accessed and modified what files. Not only does this enhance accountability, but it also enables security.
Where can you find WordPress firewall logs?
The location of firewall logs will vary significantly by the vendor. If you have your own VPS, a good first place to check is the /var/log/ directory.
If you are not sure there the solution keeps logs, defer to the provider’s documentation. If you're using Patchstack, just log in to your app to see all the logs.